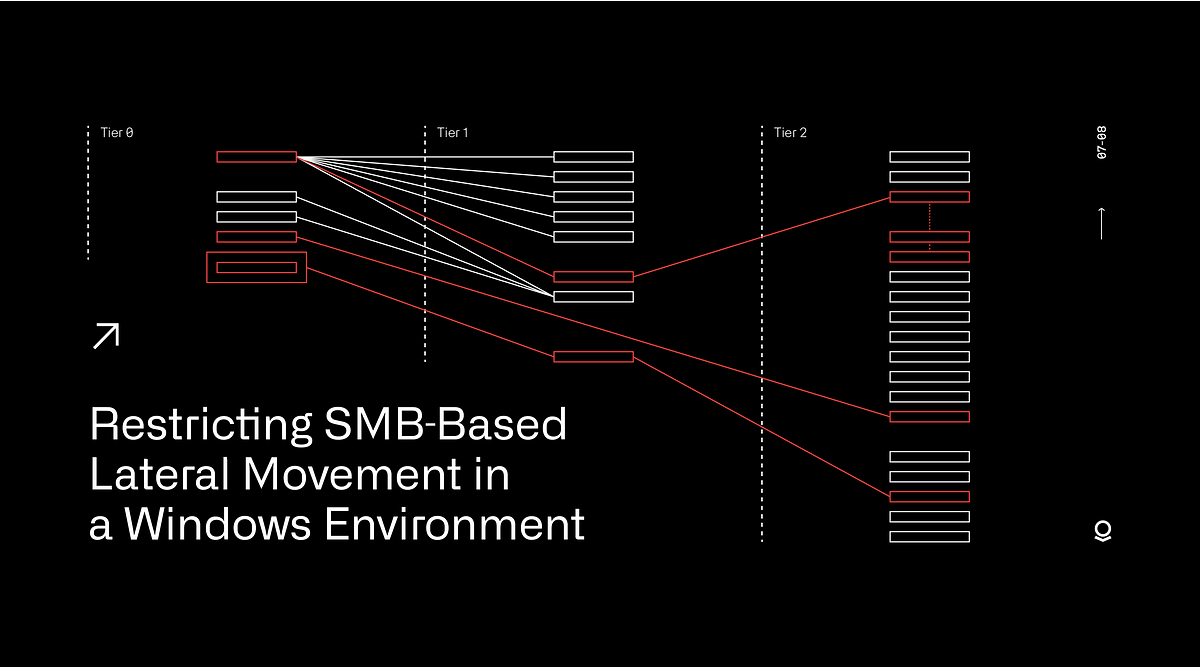
Zeyad Abdelazim Mahmoud on LinkedIn: #windows #lateral #movement #lateralmovement #exploitation #redteam… | 14 comments
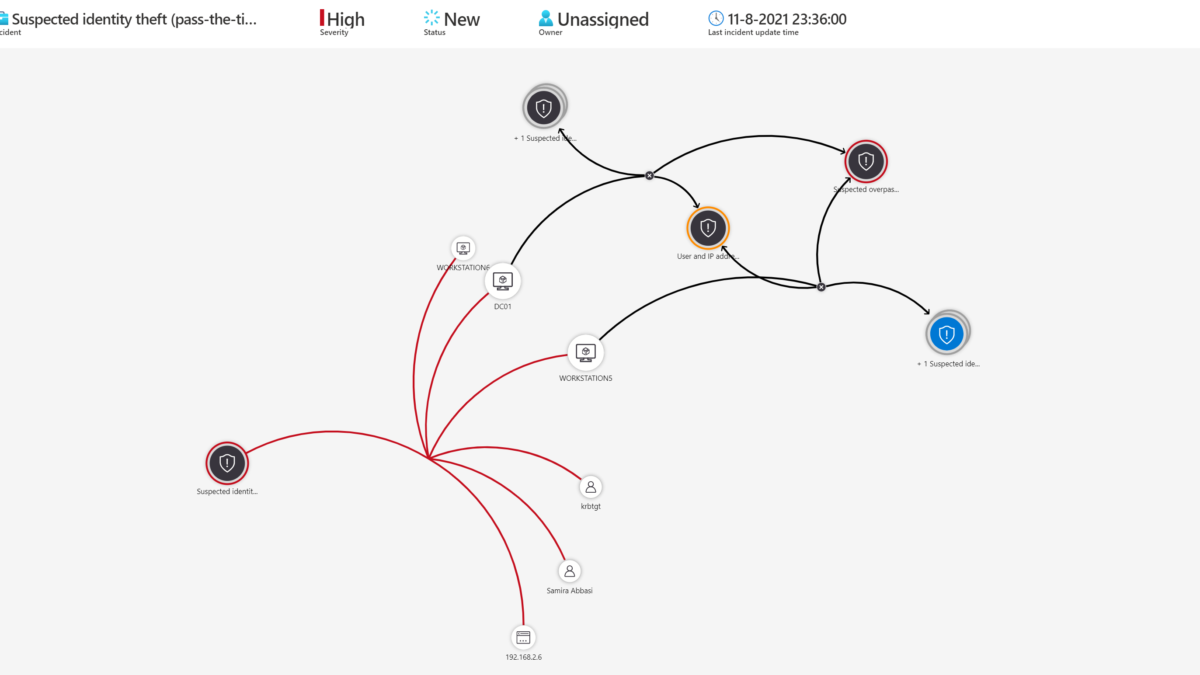
Inside Microsoft 365 Defender: Attack modeling for finding and stopping lateral movement | Microsoft Security Blog
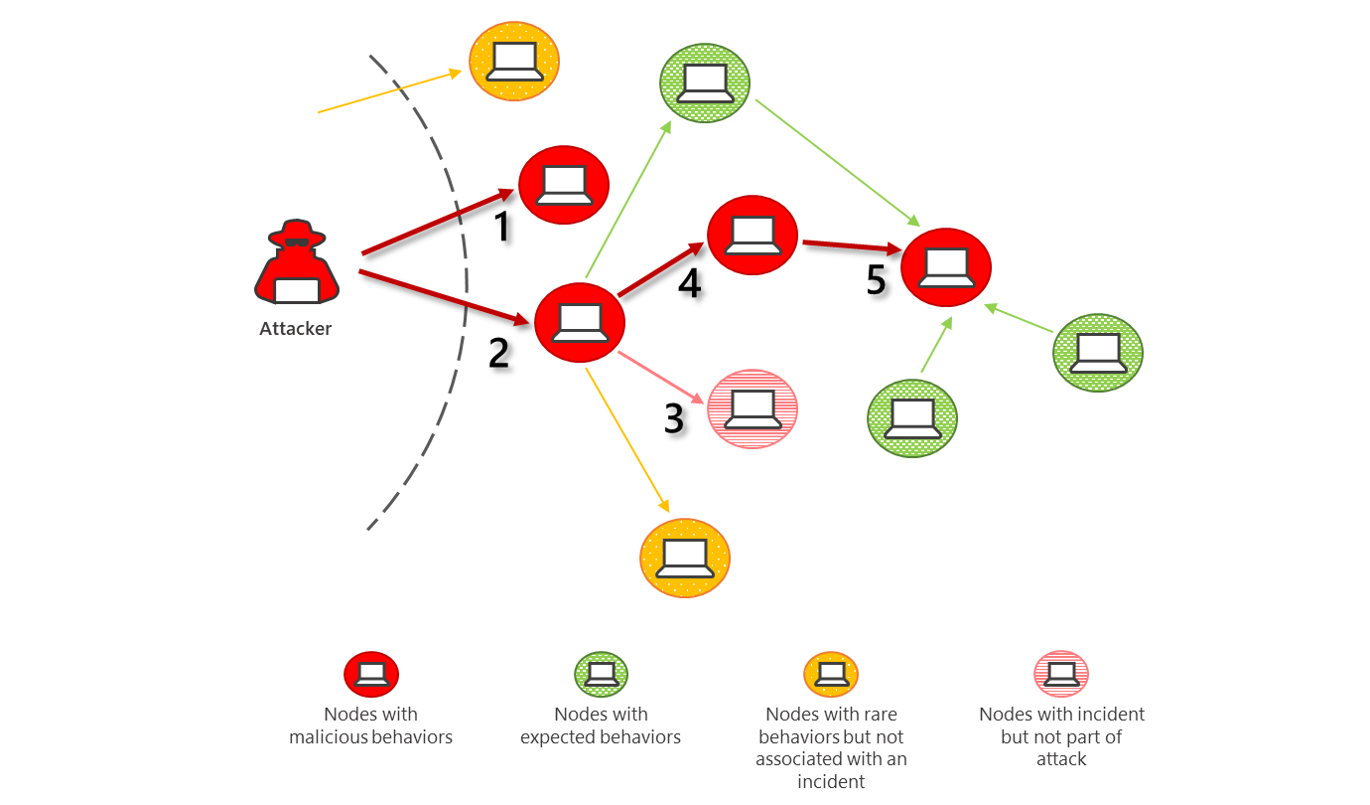
Inside Microsoft 365 Defender: Attack modeling for finding and stopping lateral movement | Microsoft Security Blog
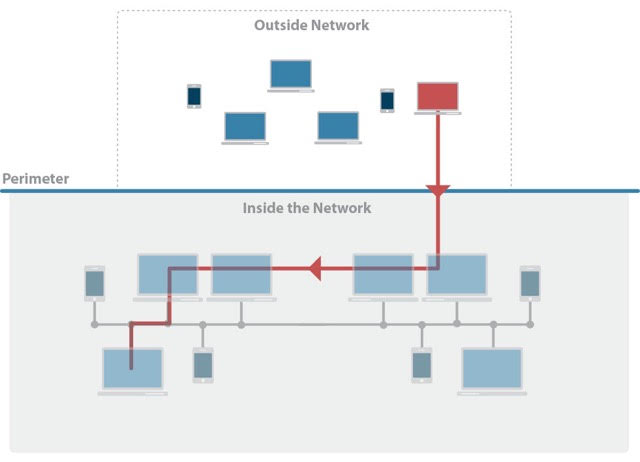
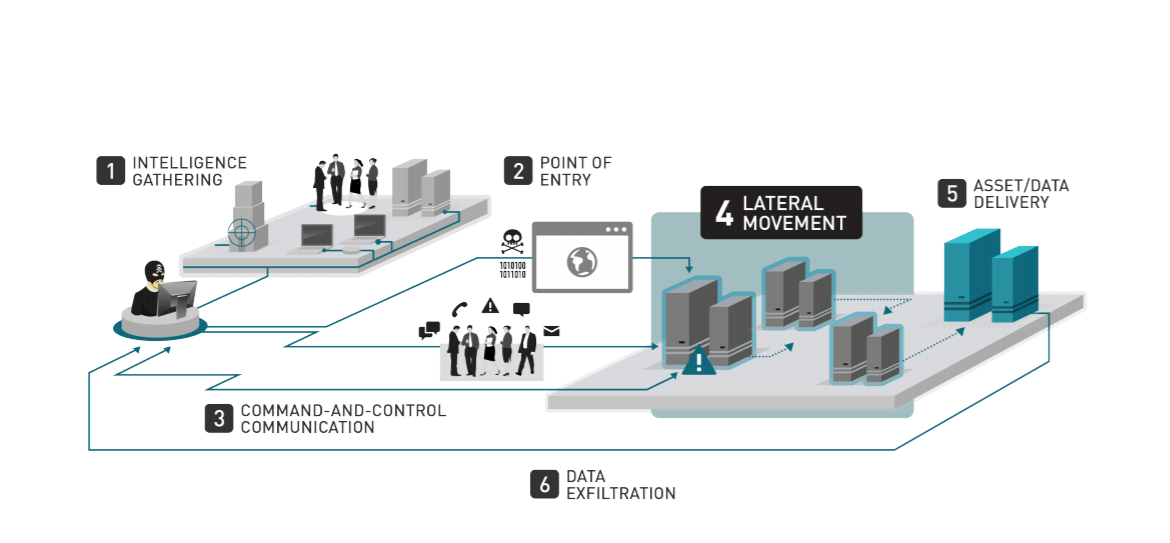
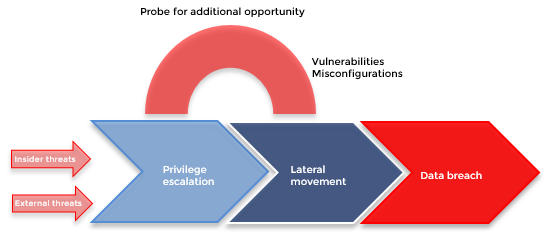
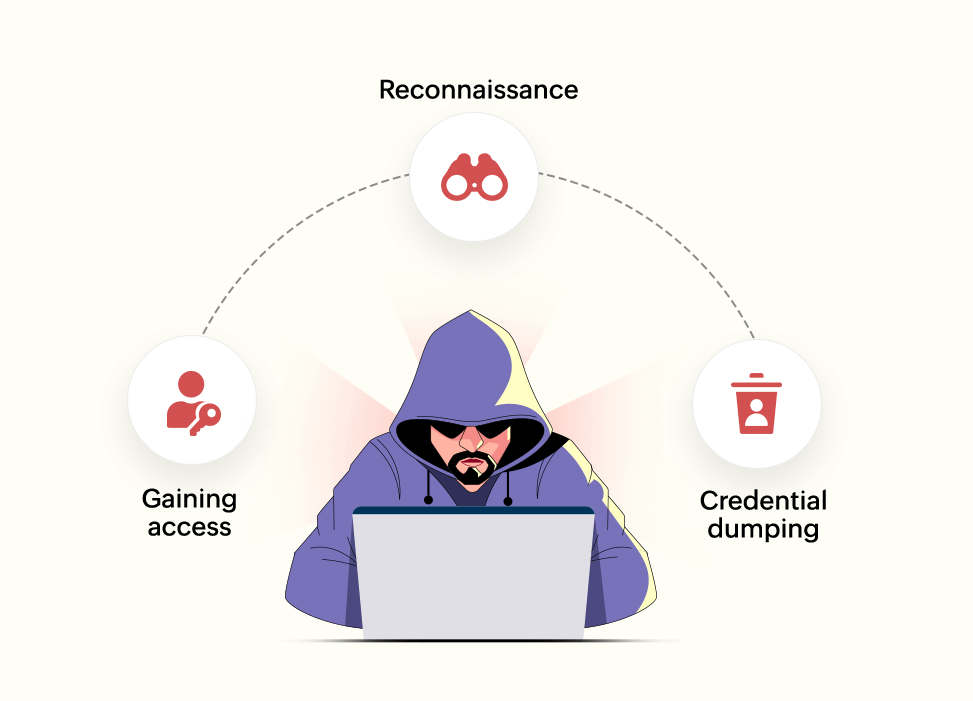
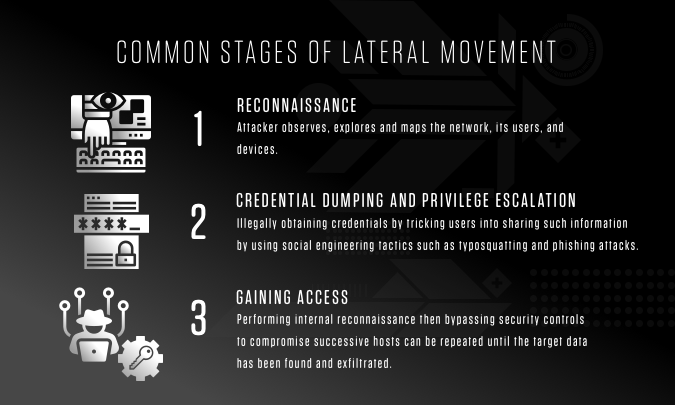
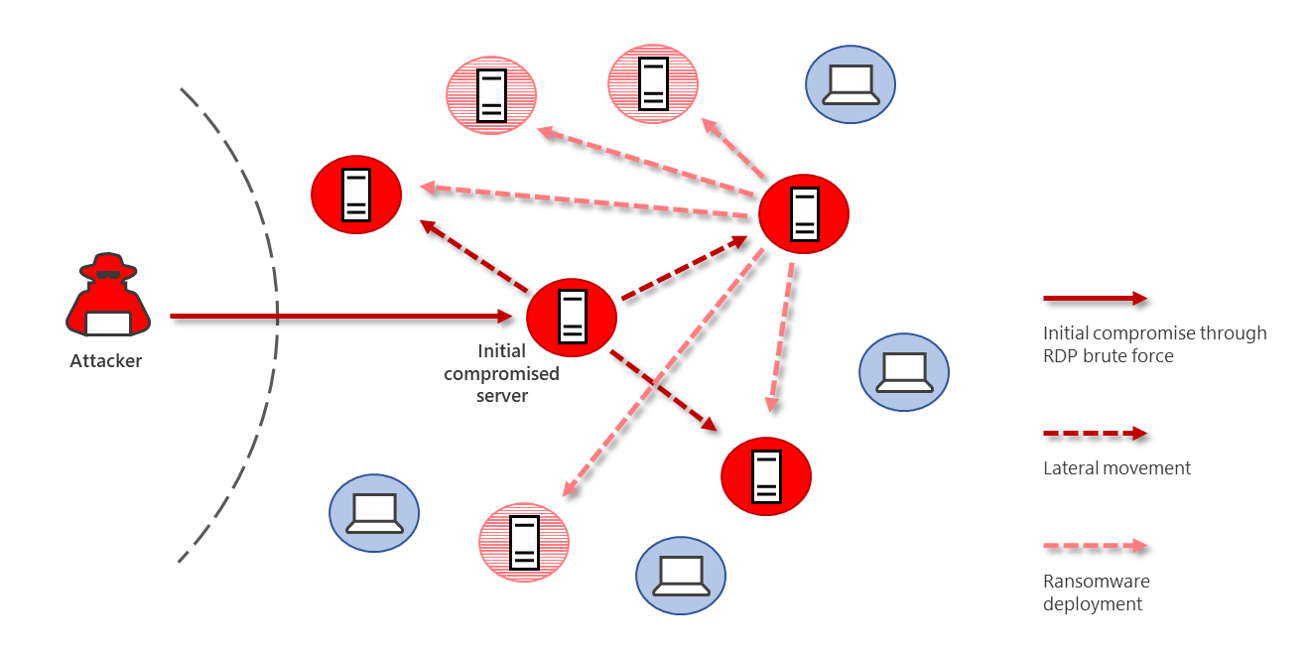
Lateral Movement: What It Is and How to Block It - Malware News - Malware Analysis, News and Indicators
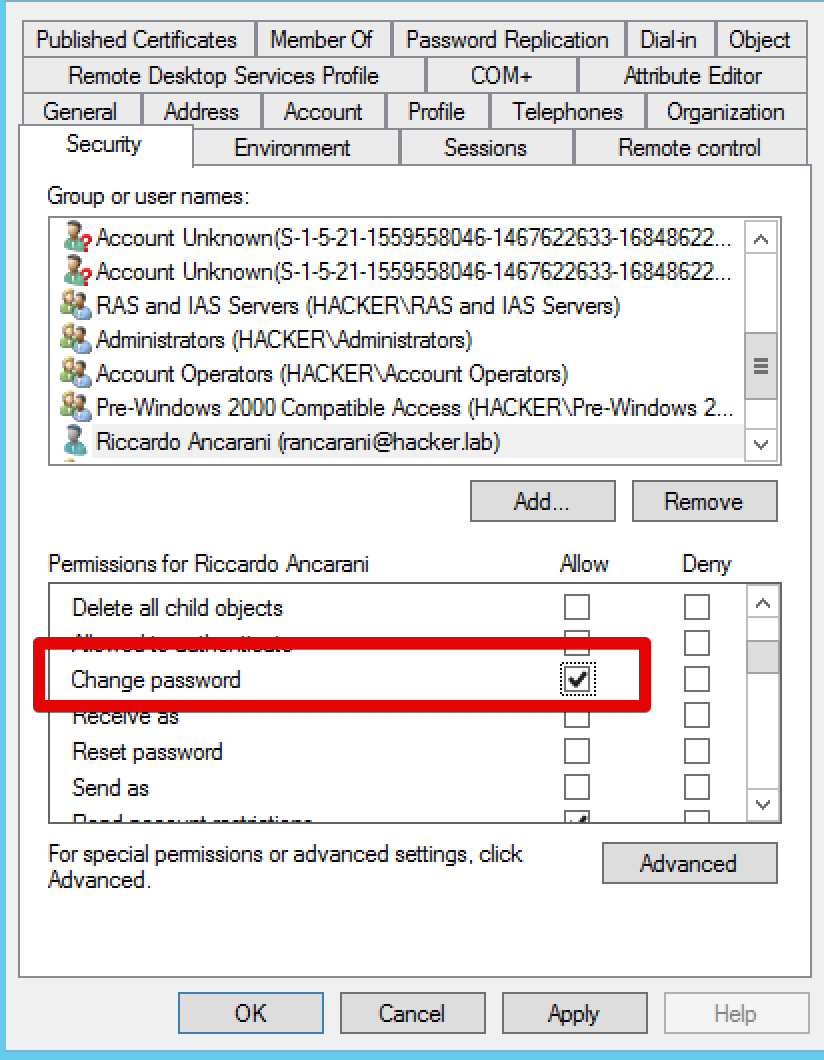
Death from Above: Lateral Movement from Azure to On-Prem AD | by Andy Robbins | Posts By SpecterOps Team Members

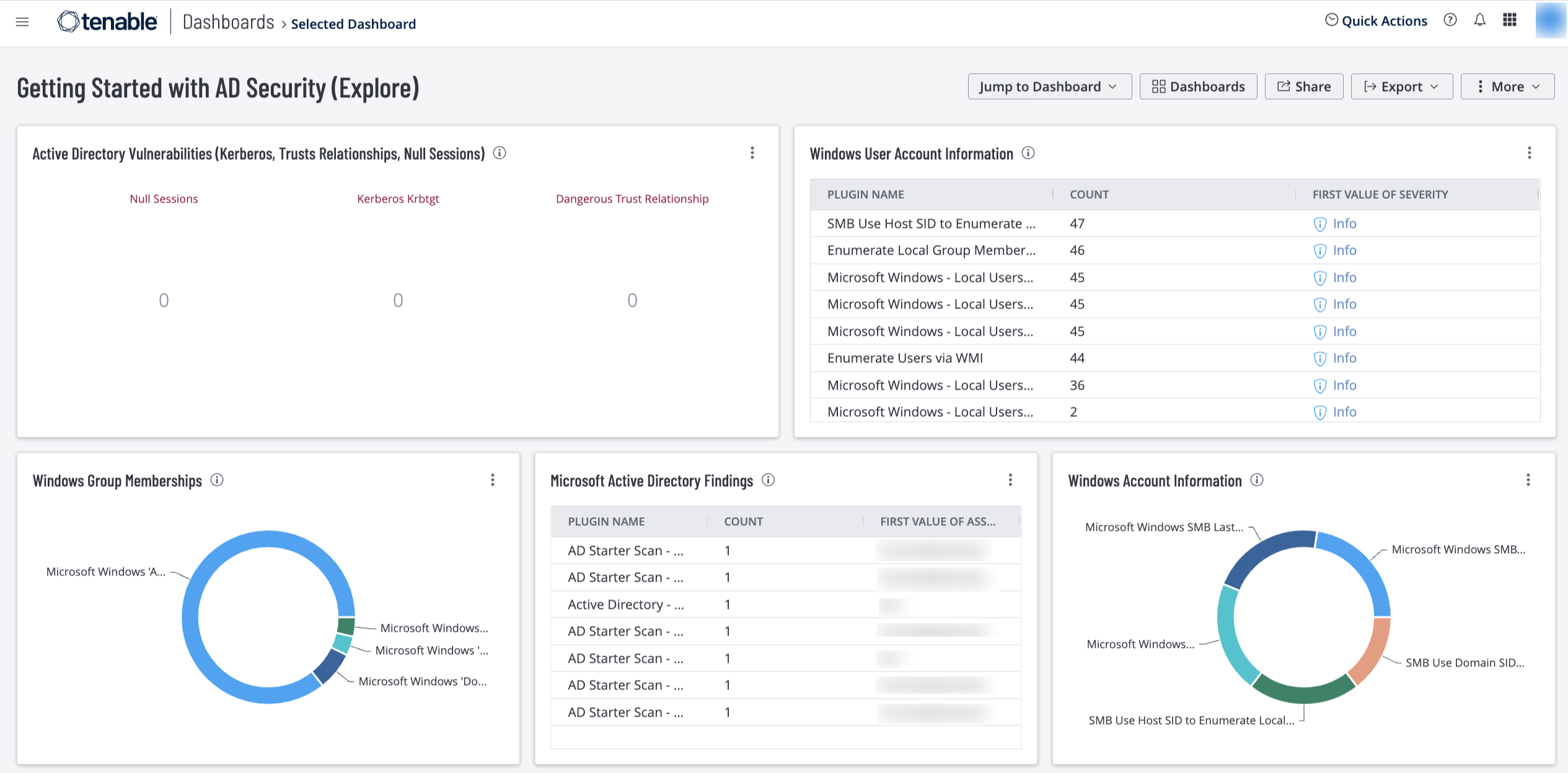
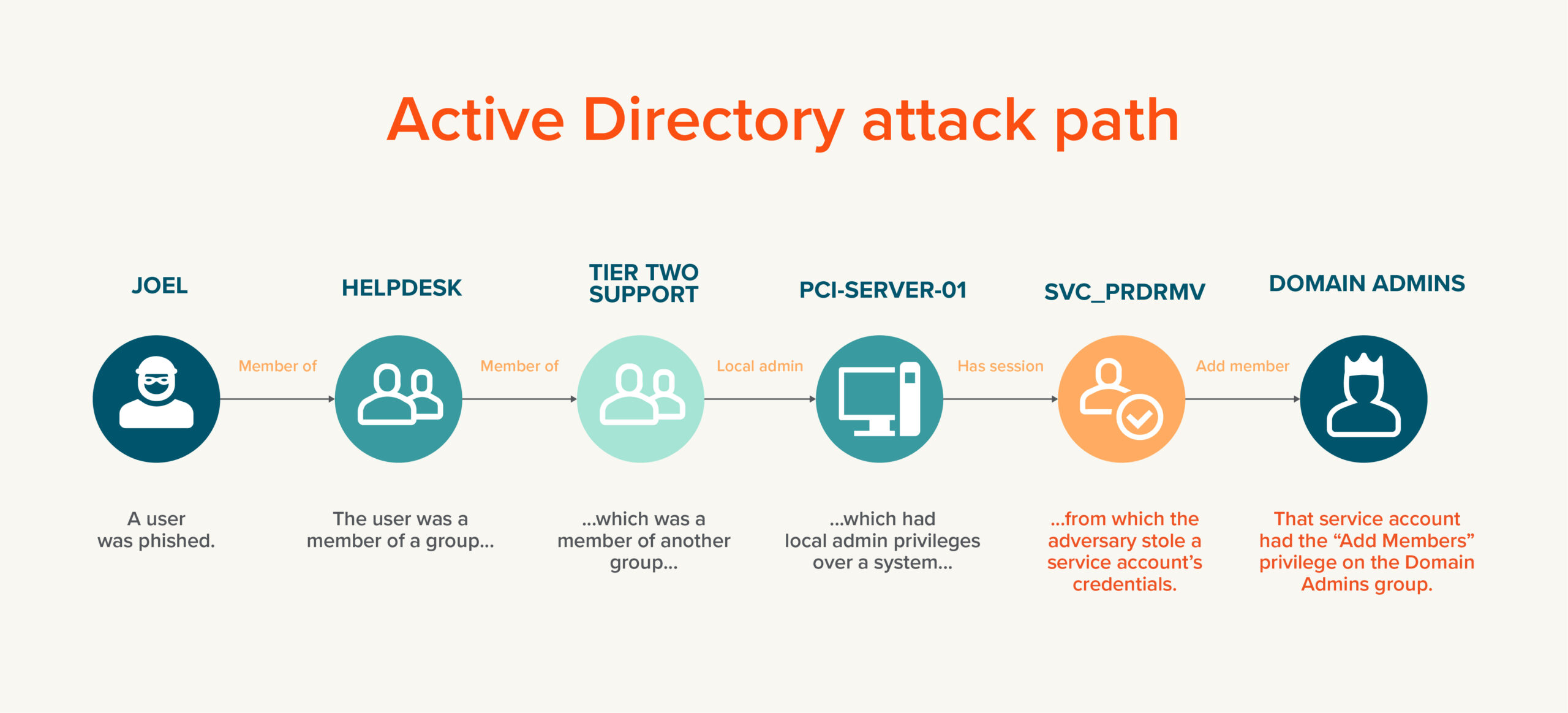
Ghost in the shell: Preventing Active Directory Lateral Movement | by Venu Vissamsetty | AttivoTechBlogs | Medium

NSA/CSS on Twitter: "- Exploit Active Directory for Lateral Movement & Credential Access - Exploit Public-Facing Servers https://t.co/W4jgubh7bX" / X